Security Testing and Assurance
Industry contributions
CyberCX’s Security testing and Assurance team are dedicated to leading the global market in innovative security testing and assurance, while nurturing the industry’s most skilled consultants to secure our communities.

Events
-
- November 2025
- Dr Joel Panther | ISACA Canberra 2025
Bytes Against Oppression: Digitally Resisting Authoritarian Regimes - Dr Joel Panther | AI & Crime Symposium, hosted by Griffith University’s Criminology Institute
AI and Crime Prevention - Ethan McKee-Harris | Kawaiicon
Breaking into Cyber Security - Ian Peters | Aotea Security
Tightly Linked: The Intersection of Cyber and Physical Security - Liam O’Shannessy | ABC’s prime-time TV series Crime Night!
- Liam O’Shannessy | Gallagher Security industry event
Cyber security in Australia and NZ through the lens of 2,500 penetration tests - James Bannan | DDD Adelaide
From Head Tattoos to Malware: A History of Steganography
- Dr Joel Panther | ISACA Canberra 2025
- September 2025
- James Bannan | CloudCon Sydney
The Great Internet Mersenne Prime Search: 30 Years of Citizen Science - James Bannan | University of Melbourne as part of the Faculty of Arts Professional Series
AI and Cyber Security
- James Bannan | CloudCon Sydney
- August 2025
- Dr Joel Panther | DEFCON 33 DCGVR Community
Do not obey in advance – Cybersecurity in the Fight Against Techno-Authoritarianism - Daniel Ting | DEFCON 33 DCGVR Community
Better AppSec through better DevEx - Liam O’Shannessy | TasICT Cyber Conference
Cyber security in Australia and NZ through the lens of 2,500 penetration tests
- Dr Joel Panther | DEFCON 33 DCGVR Community
- July 2025
- James Bannan | BSides Brisbane
From Head Tattoos to Malware: A History of Steganography - Dr Joel Panther | BSides Brisbane
Do not obey in advance – Cybersecurity in the Fight Against Techno-Authoritarianism - Johannes Van Der Merwe | BSides Brisbane
Planning a pentest: A Data-Driven Approach - Daniel Ting | BSides Brisbane
Better AppSec through better DevEx
- James Bannan | BSides Brisbane
- June 2025
- Liam O’Shannessy | Man in the Middle Podcast
STA Hack Report - Sean Titmarsh | Australian Podiatry Association Conference
An adversary’s perspective of Allied Health: How cybersecurity failures lead to compromise
- Liam O’Shannessy | Man in the Middle Podcast
- May 2025
- Liam O’Shannessy | Techpartner News industry event
STA Hack Report - Raafey Khan | Okta conference in Melbourne
Bridging the Gap: Cyber Security, IDAM, and the Evolving Threat Landscape - Jason Edelstein | Okta conference in Sydney
Bridging the Gap: Cyber Security, IDAM, and the Evolving Threat Landscape - James Bannan | BSides Adelaide
Building E8 & ISM-Compliant Master Images - James Bannan | Webinar
Microsoft Security for ISV Series: Enhanced Threat Detection & Monitoring AI Solutions
- Liam O’Shannessy | Techpartner News industry event
- March 2025
- James Bannan | AISA CyberCon Canberra
Building E8 & ISM-Compliant Master Images
- James Bannan | AISA CyberCon Canberra
- November 2024
- KS Lam | AISA Melbourne
How safe is safe? Exploiting the vitality of physical security in an ever-evolving world and its parallels to cyber security. - Carter Smith | AISA Melbourne
What you don’t know can hurt you - Jorel Paddick | Guest Lecturer at Curtin University
Behind the Firewall - DR Joel Panther | BSides Gold Coast
Stop spying on me!’ Blocking adversarial DNS requests - Jacob Larsen | BSides Melbourne
Crabby’s Credential Stuffing: How the new wave of Australian fraudsters are targeting you
- KS Lam | AISA Melbourne
- October 2024
- Liam O’Shannessy | SXSW
“From Panic to Poise – dealing with breaches
- Liam O’Shannessy | SXSW
- September 2024
- BSides Canberra
- Ayman Sagy | Presentation
V8 Internals - Shain Lakin | Presentation
Modernising Long Range RFID Hacking - David De Lille | Winner of the lock picking competition
- Ayman Sagy | Presentation
- BSides Canberra
- August 2024
- 60 Minutes
Scam HQ - Jacob Larsen | Black Hat USA | Las Vegas
From Doxing to Doorstep: Exposing Privacy Intrusion Techniques used by Hackers for Extortion - The Register
Mega money, unfathomable violence pervade thriving underground doxxing scene - Hunted TV Series
Season 3
- 60 Minutes
- November 2025

James Bannan | BSides Brisbane

Daniel Ting | BSides Brisbane
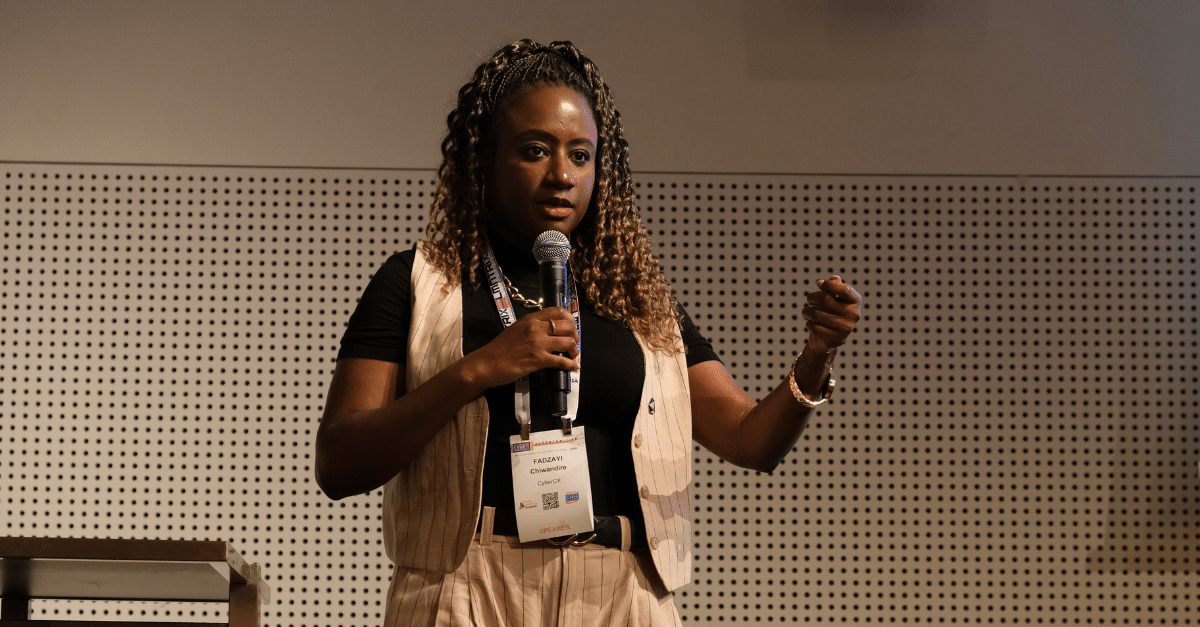
Fadzayi Moyo – Australian Cyber Con

Carter Smith – AISA Melbourne
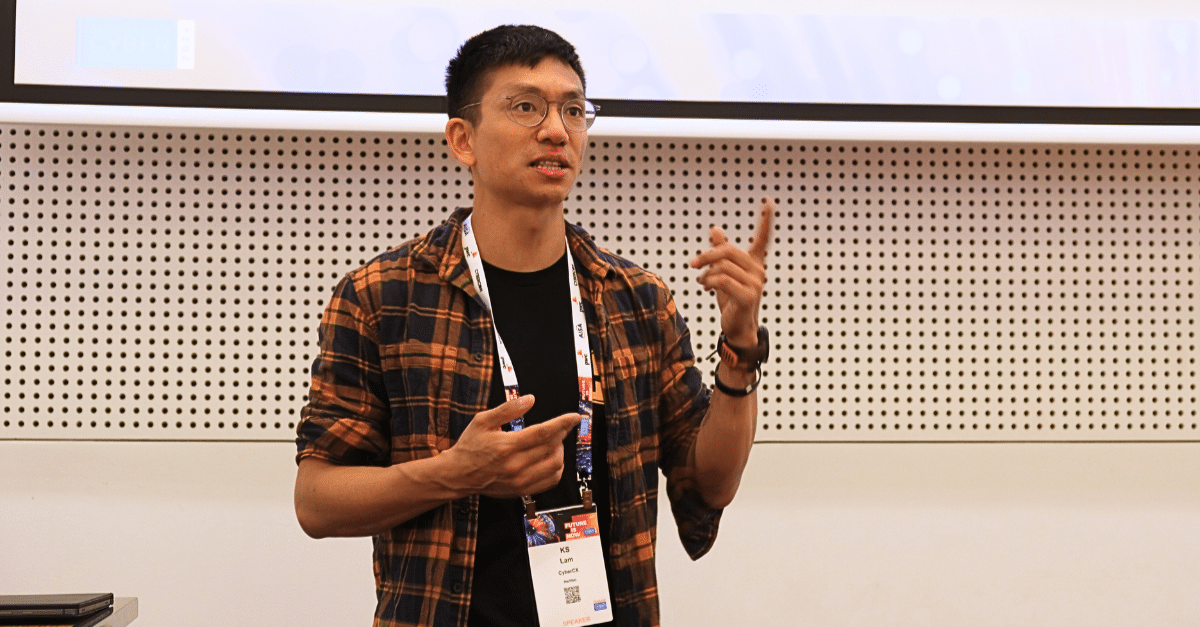
KS Lam – AISA Melbourne

Hunted TV Series – Season 3

60 Minutes: Scamdemic
Training
James Bannan
Published the Pluralsight course “Azure Infrastructure-as-Code with ARM and Bicep”
Mentored a team from Edith Cowan University (ECU) on their industry STEM project, via Practera
Jorel Paddick
Facilitating a year-long Capstone Project, focused on programming and cyber security with students from Curtin University.
James Bannan
Mentored a team from the University of South Australia on their industry STEM project, via Practera
Shofe Miraz
Organisation and coordination for Hack and Learn monthly InfoSec meetup
David Sowerbutts, KS Lam, Liam O’Brien, Fletcher Creed
Facilitated the Lockpicking Village at CrikeyCon

Blogs
- Using GitHub Copilot to accelerate PowerShell scripting
- Introducing Blade: Streamlined command-line tool for Bloodhound and Neo4j
- How 8 Bits Can Ruin Your Day
- Revisiting Conditional Access in 2025
- Introduction to PostMessage Vulnerabilities
- Shift-Left with Threat Modelling: A Quick Guide for Startups and SMEs Building Technology
- Harnessing the power of Named Pipes
- Palo Alto Cortex XDR bypass
- Privilege Elevation and Logging Bypass Vulnerabilities in OpenText Content Manager
- Zero Day RCE in NetComm NTC-221 Industrial IoT M2M LTE/4G Router
- Insights from 100 Purple Teams
Tools
PurpleOps →
An open-source self-hosted purple team management web application.
Efflanrs →
Turn your Snaffler output into a nice searchable and sortable interface.
Email Spoof Check →
Audit your domain’s SPF and DMARC configuration.
Peep →
A tool designed to hook into Windows applications and output named (and anonymous?) pipe traffic.
Pipe Client Impersonation Server →
Creates a malicious named pipe server that impersonates connecting clients and executes arbitrary commands under their security context.
Jailbreak/Root Detection Bypass in Flutter →
Frida script designed to bypass security checks that are implemented using the IOSSecuritySuite module in iOS applications and Rootbear in Android Applications.
Virtual Wireless Lab →
A series of different lab exercies with the aim to teach the fundamentals around pentesting of 802.11 networks.
Conditional Match and Replace →
A Burp extension allowing you to create match and replace operations that execute only when a condition is matched.
NSEC(3) Walker →
Automates extracting DNS zones akin to an AXFR zone transfer or a “zone dump”.